Imagine waking up to a notification that someone tried your front door handle at 3:00 AM. You haven’t lost anything, but you immediately know your locks need attention. In the digital world, many businesses remain unaware that strangers are constantly testing their windows until it is too late.
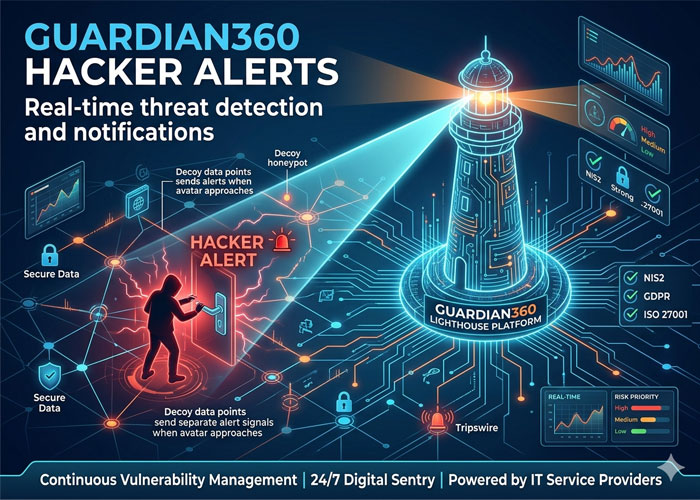
Criminals rarely target specific companies manually; instead, they use automated programs to rattle thousands of digital doorknobs simultaneously. Guardian360’s Hacker Alert system functions as your invisible tripwire against this activity. Deployed through the Lighthouse platform and managed by your IT service provider, these alerts tell you exactly who is looking for a way in—before they find one.
True safety requires more than just a strong password. With real-time threat detection, you gain the visibility needed to stop a curiosity from becoming a catastrophe.
How Continuous Vulnerability Management Acts as Your 24/7 Digital Sentry
Imagine checking if your front door is locked only once a year on January 1st. For the rest of the time, you just assume you are safe while family members come and go. Many businesses operate this way, relying on annual manual checks for identifying web application security flaws. By the time the report arrives, the information is often outdated. A continuous vulnerability management system solves this by trading that yearly snapshot for a 24/7 security feed.
Software changes constantly—updates run, features are added, and settings shift. Each change is like a home renovation; sometimes, it accidentally leaves a window unlatched. Since you cannot manually check every lock every hour, automated scanning acts as your digital building inspector. Guardian360’s Lighthouse platform quietly rattles every doorknob and tests every latch on your network, finding these hidden entry points before a stranger does.
Shifting to this always-on approach offers distinct advantages over the traditional method of vulnerability scanning vs manual security audits:
- Frequency: Scans happen daily rather than yearly, closing gaps faster.
- Accuracy: Automation eliminates human fatigue and oversight.
- Speed: You receive instant alerts instead of waiting weeks for a compiled report.
From Detection to Action: Decoding the Anatomy of a Real-Time Hacker Alert
Just like a silent alarm notifies the police when an intruder steps on a sensor, modern cybersecurity uses digital tripwires to spot danger instantly. Guardian360’s Hacker Alert system places honeypots—digital decoys that appear as valuable targets such as file servers or databases—inside your network. These decoys have no legitimate business purpose, so any interaction with them is by definition suspicious. When an intruder touches one of these traps, how do real-time threat notifications work becomes clear: the system triggers an immediate alert to your IT service provider, identifying exactly where the unauthorized activity is happening without the intruder realizing they have been spotted.
Speed serves as your most critical advantage because intruders need time to move from a generic entry point to your valuable files. Traditional monitoring might leave a breach unnoticed for weeks, giving criminals ample time to explore, but reducing incident response time with alerts shrinks that window down to minutes. This rapid warning system transforms a potential disaster into a manageable event, allowing your IT partner to lock the digital doors before anything sensitive is taken.
Receiving a notification does not mean you need to panic or decipher complex computer code. The Lighthouse dashboard acts as a translator, showing you how to interpret cybersecurity risk reports by categorizing issues simply as high, medium, or low urgency. Think of this prioritization like a car dashboard; a flashing red oil light demands immediate action, whereas a yellow washer fluid light can wait, ensuring you focus your energy only on the problems that truly threaten your operations.
Once you understand the urgency of a specific threat, the next logical step involves testing your defenses against a simulated attack to prove they hold up. While alerts tell you what is happening right now, proactive scanning predicts what could happen tomorrow.
The Power of Automated Vulnerability Scanning in Preventing Unauthorized Data Access
Most people wouldn’t install a new alarm system without testing it first to ensure it actually triggers. Automated vulnerability scanning works on the same principle—it acts like a digital building inspector hired to find unlocked windows before a real criminal does. By continuously probing your network for known weaknesses, you gain visible proof of where your defenses hold up and where they need reinforcement. Guardian360’s scanning engine, built on exploit-focused technology, goes beyond simply listing vulnerabilities—it validates whether they are actually exploitable, highlighting one of the primary automated vulnerability scanning benefits: discovering real risks while you still control the outcome.
Waiting for a breach to occur is the most expensive way to identify a security hole. Instead of reacting to a disaster, these tools continuously probe your systems to ensure that sensitive customer information stays out of the wrong hands. This shift from passive defense to active scanning is critical for preventing unauthorized access to business data, as it closes the specific entry points hackers rely on, effectively saving you the reputational damage and financial cost of a public data leak.
When evaluating the top features of managed security platforms, prioritize systems that offer:
- Exploit-based scanning: Validation that goes beyond detection to confirm whether a vulnerability is actually exploitable.
- Automatic compliance reporting: Proof that you are meeting industry safety standards such as NIS2, GDPR, and ISO 27001.
- Microsoft 365 security insights: Visibility into your cloud email and collaboration environment, often the primary target for phishing and account compromise.
- Actionable remediation guidance: Clear instructions on how to fix the problems found, prioritized by business risk.
With these protections in place, your focus can shift from technical survival to regulatory assurance.
Achieving NIS2, GDPR & ISO 27001 Compliance Through Better Monitoring
Legal frameworks like the GDPR, the European NIS2 Directive, and standards such as ISO 27001 require you to demonstrate “reasonable care” in protecting information assets. With regulations like the Dutch Cyberbeveiligingswet (implementing NIS2) and DORA for financial services now in effect, data safety has become a continuous obligation rather than a yearly checklist. By implementing constant oversight through a platform like Lighthouse, achieving compliance through monitoring becomes a natural byproduct of your operations rather than a panicked audit scramble. This digital paper trail proves to regulators that you are actively watching the gate, protecting your business from hefty fines while securing customer trust.
Effective security means catching attempts before they cause damage. Just as a rattling doorknob alerts you to an intruder, specific digital anomalies indicate danger. Understanding what are early warning signs of a cyber attack—such as unexpected login attempts, sudden file changes, or unauthorized interactions with honeypots—allows you to intervene immediately. These silent alarms give you the upper hand, transforming a potential crisis into a manageable event before data actually leaves your building.
Clients inherently trust partners who take security seriously. Integrating continuous monitoring creates a foundation of accountability that serves as the cornerstone of any comprehensive IT security compliance guide, ensuring you are never caught off guard.
Your Action Plan: Transforming Cybersecurity from a Stressor into a Strength
Cybersecurity no longer needs to feel like a guessing game. By understanding how Guardian360’s Lighthouse platform works, you have turned the lights on, transforming invisible risks into clear, actionable insights. Instead of worrying about the unknown, you can now focus on mitigating internal and external digital threats with clarity. You aren’t just reacting to noise; you are proactively managing your safety.
Turn this knowledge into immediate action with a simple plan:
- Ask your IT service provider about Guardian360’s Lighthouse platform and request an initial vulnerability scan of your environment.
- Designate a “First Responder” in your team who receives and acts on Hacker Alerts and vulnerability reports.
- Review your compliance posture against NIS2, GDPR, and ISO 27001 using the Lighthouse dashboard’s built-in compliance monitoring.
Effective security is a habit, not a one-time fix. Routine security updates and consistent monitoring are the foundation of best practices for cloud security posture management. With Guardian360 and your IT partner by your side, you stop being a passive target and become an active guardian of your business data. You are now ready to stay one step ahead.